SOLUTIONS
KEYPASCO ENTERPRISE
Keypasco Enterprise helps organizations establish a trusted identity authentication mechanism, protect data, enhance account security, and meet compliance requirements.

Making Security Part of Your Corporate Culture
Cybersecurity should not be solely the responsibility of the IT department, it should be part of every employee’s daily routine. From logging into systems and connecting to VPNs, to accessing sensitive data, every action carries potential risk and is an opportunity to strengthen security culture. Keypasco Enterprise empowers companies to embed security into authentication practices, turning protection into a habit and creating sustainable, organization-wide cyber resilience. Only by internalizing security as culture can businesses build a truly trustworthy foundation for digital operations.

Seamless System Integration

Anti-phishing Device Authentication

Enterprise Identity & Access Control

Compliance-ready Security
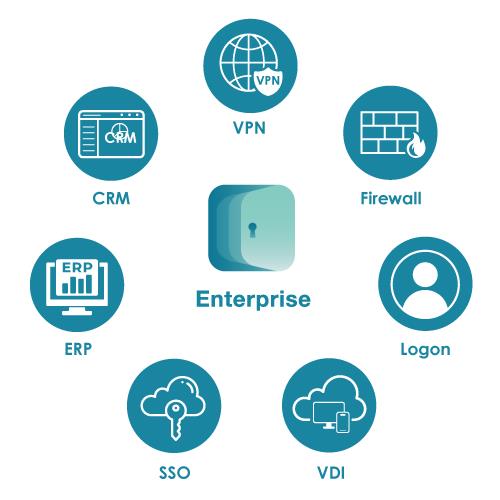
Fast Integration Across Enterprise Systems
Keypasco Enterprise provides modular authentication solutions that seamlessly integrate with VPN, CRM, ERP, Windows logins, Office 365, intranet portals, and cloud applications. With APIs and standard protocols, enterprises can deploy anti-phishing authentication without system reconstruction, enhancing security while optimizing user experience.
The system supports both on-premises and cloud deployment, meeting the stringent IT requirements of sectors like finance and government. With High Availability (HA) and Disaster Recovery (DR) designs, authentication remains stable and resilient. Keypasco also offers one-stop deployment packages for Windows/Linux environments, enabling rapid deployment of secure authentication platforms while reducing costs and dependency.
Keypasco Certificate-free + Anti-phishing MFA
Keypasco MFA uses a certificate-free, phishing-resistant approach, combining patented two-channel authentication, device fingerprints, proximity checks, time/location controls, risk management, and private key splitting to deliver seamless, secure online and offline OTP.
Patented Two-channel Structure with 'Sign What You See' & Device Fingerprints
Two-channel Structure & Sign What You see
Keypasco’s Two-channel authentication splits login and verification across two devices for stronger security. A second-channel request enables “Sign What You See,” reducing man-in-the-middle risks.

Device Fingerprints
Keypasco identifies trusted devices and detects anomalies by dynamically collecting unique hardware, software, and firmware attributes.

Additional Keypasco MFA Protection Features

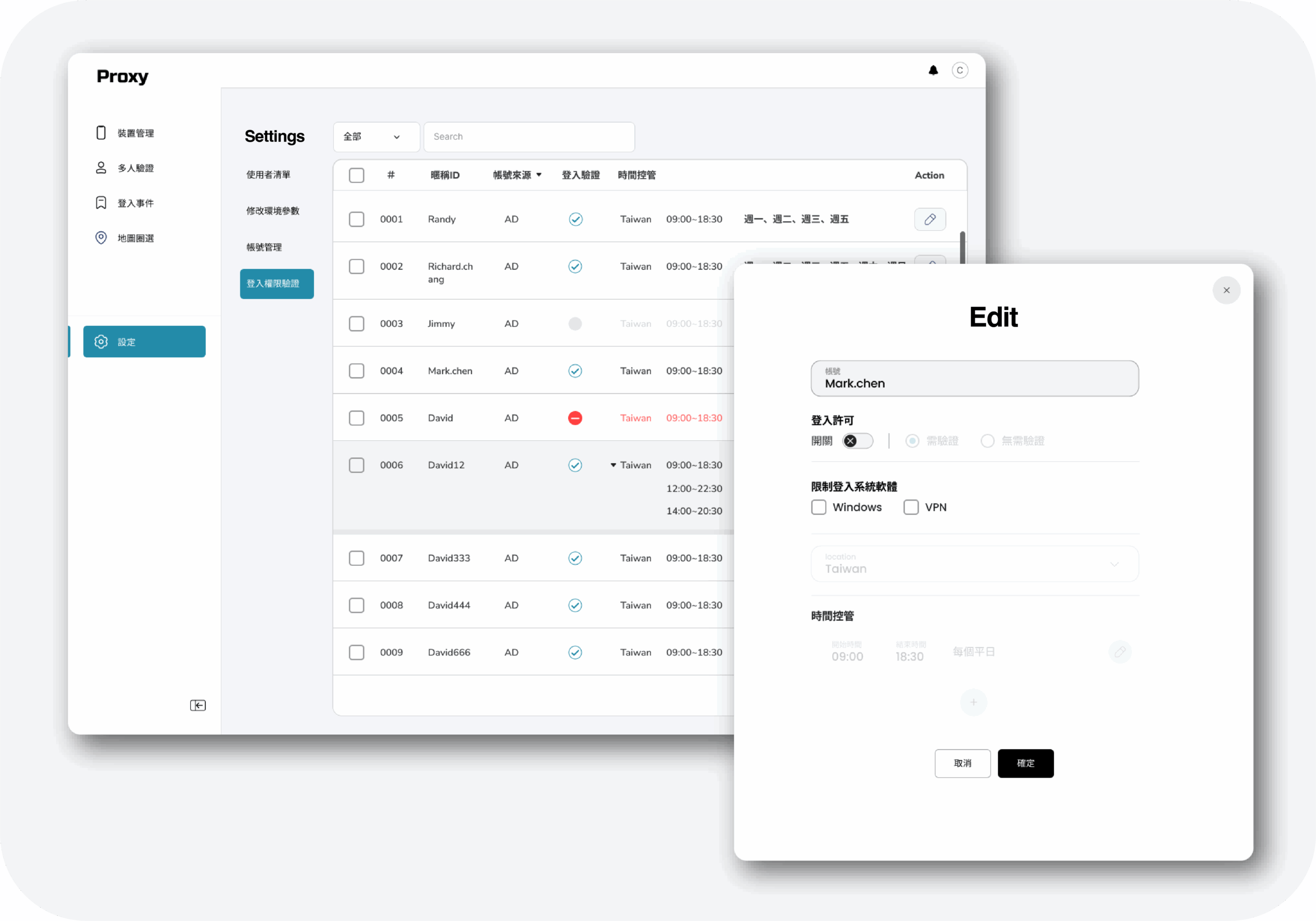
Time Management
Restrict verification to a set time period

Geolocation Management
Restrict verification to a specific location

Risk Management Engine
Rule-based intelligent risk management using behavioral data to continuously strengthen security

Proximity
Verification via Bluetooth, NFC, USB, or wireless-enabled secondary devices (e.g., credit card)

Split PKI Sign
Private key splits, encrypts, and stores in app and server — never fully retained.

Online/Offline OTP
One-time password authentication for both online and offline scenarios
Flexible Deployment
Enterprise-grade Identity and Access Management
Keypasco with a built-in policy engine, administrators can create dynamic authentication rules based on user identity, access time, location, and device status—enhancing both security and flexibility.

Compliance-ready Security for Enterprises
With increasing regulatory pressure, enterprises and government agencies face both technological and compliance challenges. Keypasco Enterprise helps organizations align with identity authentication, anti-phishing, and access control requirements set by authorities such as the Ministry of Digital Affairs and the Financial Supervisory Commission.
The system is aligned with global standards such as CISA Zero Trust Framework, NIST SP 800-207, and ISO 27001. It includes built-in audit logging, with geolocation awareness, organizations can automatically adapt access policies to contexts, strengthening auditability, risk control, and zero trust implementation.
Note: The system is continuously evolving to meet CISA and other international standards. Some advanced authentication features are still under construction and testing.
Keypasco Enterprise Deployment Overview
Before deploying Keypasco Enterprise, employees typically rely on account-password logins to access internal systems and applications—making them vulnerable to account hijacking and man-in-the-middle attacks. Enterprises seeking stronger authentication and security controls can quickly integrate existing systems with Keypasco Enterprise to implement customized Multi-Factor Authentication (MFA).
Keypasco Enterprise supports a wide range of authentication methods, including device binding, Two-channel Structure, geolocation and time-based restrictions, proximity authentication, and risk management engine. After deployment, employees can maintain their familiar login process, while Keypasco’s anti-phishing defense and risk control technologies run seamlessly in the background—significantly strengthening enterprise access security without disrupting the user experience.

Recommended Server Specifications
Deployment Options
Cloud (AWS) or On-Premises
Supported Databases
Support Microsoft SQL Server、PostgreSQL、SQLlite
Supported Server Operating Systems
Supports Commercial RedHat 8 & 9, Ubuntu 18 – 24, Windows Server 2016 or later
Supported Mobile OS
Android 7 or later, iOS 12 or later
Supported Browsers
Firefox, Google Chrome, Microsoft Edge, Safari
LATEST NEWS
Master Cybersecurity Trends to Build a Foundation of Competitiveness

Software Security Reminder and Announcement of Company English Name Change
※ Recently, we discovered on the VirusTotal website that malicious software has fraudulently used code-signing certificates containing our company’s name. We kindly remind all users not to download any software that is not officially provided by our company, in order to avoid potential security risks. In addition, due to the

Remote Work, Wide Open Doors: The Real Playbook for Securing a Remote Workforce
As digital transformation and remote work accelerate, the attack surface expands faster than most security teams can keep up. Home offices, personal devices, and public Wi‑Fi all introduce new vulnerabilities, and entry points that attackers are quick to exploit Organizations that still rely on password‑only authentication are leaving the door

Fortify Your Enterprise: Top 10 Common Methods + Practical Zero Trust & MFA Defense
Hacker attacks are evolving quickly, shifting from isolated breaches to complex intrusions across systems and identities. Implementing Zero Trust Architecture (ZTA) and Multi-Factor Authentication (MFA) is now essential for robust cybersecurity.” From the perspective of a cybersecurity service provider, this article summarizes the ten most common attack techniques, along with

Feature One

Feature Two

Feature Three
Strengthen Your Identity Authentication.
Elevate Enterprise Security.
Keypasco is delighted to share more about our exclusive technologies and products with you! Tell us your needs and goals, and let Keypasco deliver the most suitable solution—becoming your dedicated identity authentication technology advisor.
如果您想問技術相關問題 請點我